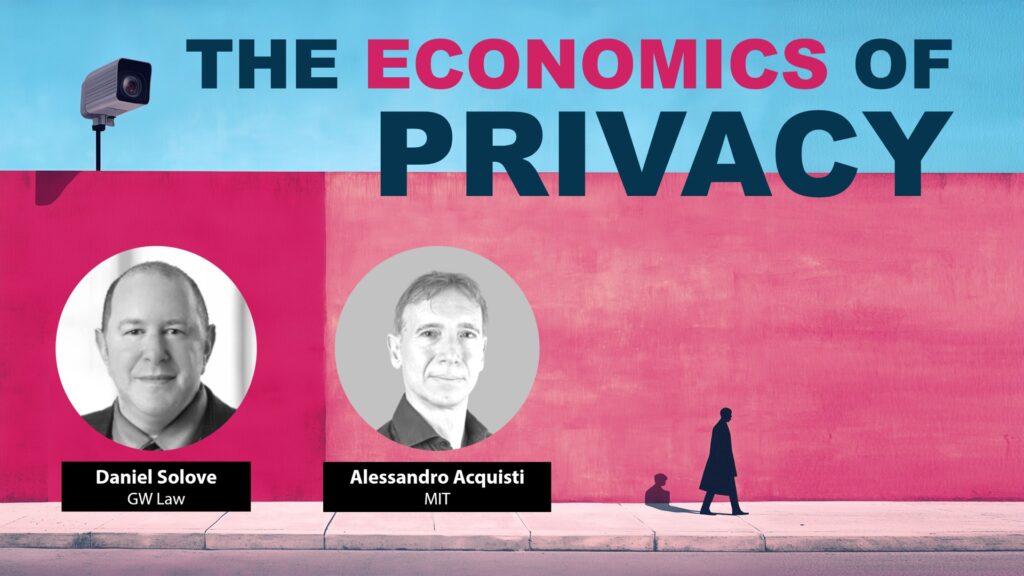
Daniel Solove interviews Alessandro Acquisti (MIT) about his pathbreaking work on the economics of privacy. Topics include the privacy paradox, the value of personal data, attitudes and behaviors, and the impact of laws.
The Economics of Privacy – Video